

Companies put lot of effort, money and time to mange information, which includes financial transactions, documents, sensitive information etc. Regulations and laws force companies to follow accounting and other standards to manage and file information
in standard reports like financial statements etc. If there are discrepancies then legal authorities request audit to make sure there is no fraud, mis-representation etc.
In a company following teams look at enterprise data to make sure information and controls are adequate and represented correctly.

Audit is a process which provides assurance that management has presented a ‘true and fair’ view of a company’s financial performance and position. Audit process typically assess a given area and express opinion whether it is presented accurately. There are following types of audits:
Audit is a costly and lengthy process, which diverts company's resources, damages reputation, invokes legal action etc. To avoid audit companies setup strict business and ethical policies and insure proper internal controls are in place. Companies setup appropriate data access, risk management, communication and monitoring strategies.
Solution enables companies to leverage Big Data to store information like financial transactions, documents from various systems at central repository, allow easy and fast exploration, find gaps, reconcile and automate the process. It allows easy UI for audit, risk and compliance team to perform their tasks easily.
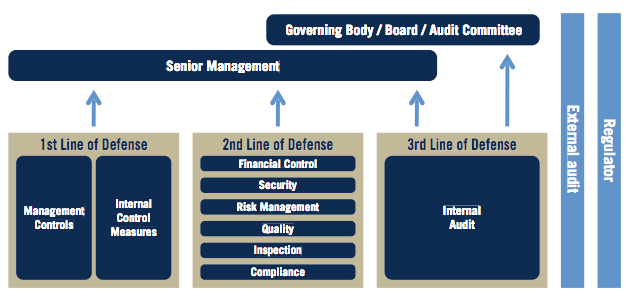
Audit defense solution follows three lines of defense model to enable internal audit, risk, compliance, control and management teams to make sure there are no gaps and in-consistencies.
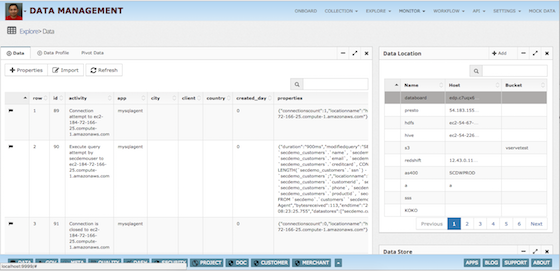
Audit defense solution enables stakeholders to explore large amount of data from central repository. Data analysis provides insight to detect fraud, issues, risks and other compliance errors.


Auditors look extensively at company's assets, processes and systems and perform following testing.
Audit Defense solution allows internal audit teams to explore and conduct testing easily with an interactive UI.
Explore data sets easily using an intuitive data explorer.
Explorer also provides features like highlighting rows/cells, adding tags and notes, which could be used for capturing additional information about data at cell level.
Audit defense solution provides dashboard for internal audit and risk teams to see the following:
Data Reconciliation feature enables comparison of two data sets, which results in matching and non matching records. Data reconciliation can be done at various places, for example:
1 Source to target matching - In a data pipeline end step could be provisioned to check if target data store reflects all the source records. If records match that means data pipeline has properly processed all the records,
otherwise something went wrong during the process.
2 Matching records from different data sources - Data validation/reconciliation can be done between two data sources, which could be built by separate data pipelines.
Data reconciliation can be automated to run at pre defined period to check the data consistency.
Drill down feature allows checkin what parent table records were used in formation of subject table's mismatched record. This helps in finding the gaps easily.
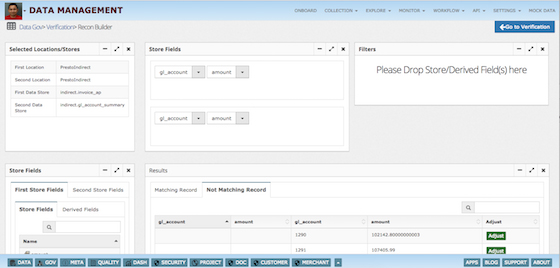
Data adjustment feature allows exploration of manually adjusted data sets before reporting. It also captures audit information like who changed, when, what changed, why change was done and who approved the change.
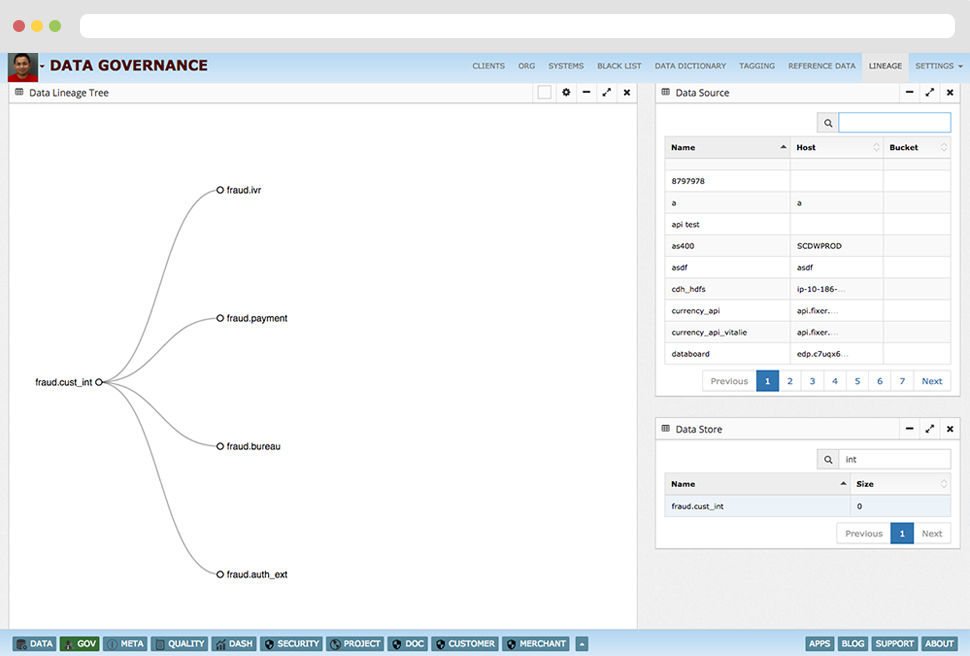
Lineage feature allows visual tracing of data sets with clear business friendly data definitions.

Audit process is costly and time consuming, when companies are large with complex hierarchies it becomes even more necessary to employ automated checks to avoid gaps.
Audit, compliance and risk teams explore enterprise data sets/systems to find gaps and inconsistencies. Building a central repository on Hadoop/Big Data enables them to automate these processes to generate alerts, reports
on periodic basis. These reports and dashboards can be shared with executive management, internal or external audit teams or regulators.
Audit Defense solution allows automation of audit process steps like: